Do you want to purchase an SSL certificate? Then, the first thing you need to do is to have a Certificate Signing Request (CSR) and a private key.
Read on to learn how to create a CSR and a private key using OpenSSL.
Overview of the OpenSSL Certificate Signing Request (CSR) generation process
Before we go into details of OpenSSL CSR generation, let’s get the definitions out of the way. See the following sections for those.
What is OpenSSL?
OpenSSL is an open-source CLI tool used to create private keys, CSR, and self-signed certificates, install SSL/TLS certificates and determine certificate information. It uses a cryptographic library to implement Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocols in an open-source manner.
If you're running a UNIX-based operating system like Linux or macOS, you’ll already have OpenSSL installed.
In contrast, if you want your OpenSSL CSR creation to happen on a Windows PC, you can use the Linux subsystem in Windows 10 or install Cygwin.
What is a private key?
Your first step toward getting an SSL certificate is to create a private key. The private key is required for all TLS/SSL certificates. It’s a file used to encrypt and decrypt messages sent from your server to clients.
During the OpenSSL CSR creation process, you, the certificate owner, create your own private key. The SSL provider that issues your certificate doesn’t generate or own that private key. In other words, no one outside of your business has access to your private key — nor should they.
Highlight: Remember your private key is private. Do not send your private key over the internet (e.g., via unsecured email), as that may compromise the security of your certificate.
What is a Certificate Signing Request (CSR)?
A Certificate Signing Request (CSR) is a set of encrypted text sent to a Certificate Authority (CA) when a user requests a certificate, such as an SSL/TLS certificate. This file contains information such as the domain and organization name, country, and location.
The CSR is a public key generated on your server according to your server software's instructions. If you don’t have SSH access or access to your servers, contact your web hosting provider to generate a CSR for you.
What is an SSL certificate?
SSL certificates are pieces of code on your web server that encrypt information transmitted over the internet. When someone accesses your secure website through a web browser, the certificate encrypts the connection, much like sealing a letter in an envelope before it is mailed.
An SSL certificate is issued by a third-party certificate provider (like Comodo) to verify your organization’s information and provide you with a unique certificate. Of course, you can self-sign certificates as well, but you can only use them in test or development environments since browsers don’t trust them.
OpenSSL CSR generation step-by-step procedures
As a system administrator, do you need to generate an OpenSSL CSR for your website? The sections below cover the steps you can follow for generating an OpenSSL CSR for your site.
How to check your OpenSSL version
Before getting into OpenSSL CSR creation, check the OpenSSL you're using. The first version of OpenSSL to support TLS 1.1 and TLS 1.2 was version 1.0.1e. So, it’s helpful to know which version of OpenSSL you're running for TLS and seeking assistance from customer support.
Issuing the command to display your OpenSSL version
On your command shell, type the command below to find out the version of OpenSSL you’re using:
openssl version -a
If you need advanced information about your OpenSSL installation, use the -a switch. That’ll display details like those shown in the following partial coe snippet examples:
OpenSSL 1.1.1f 31 Mar 2020
- The version number and release date of the OpenSSL installation.
built on: Tue May 3 17:49:36 2022 UTC
- The options that were built with the library.
OPENSSLDIR: "/usr/lib/ssl"
- The directory that stores all your certificates and private keys.
Full code snippet example
root@nxsupport:~$ openssl version -a
OpenSSL 1.1.1f 31 Mar 2020
built on: Tue May 3 17:49:36 2022 UTC
platform: debian-amd64
options: bn(64,64) rc4(16x,int) des(int) blowfish(ptr)
compiler: gcc -fPIC -pthread -m64 -Wa,--noexecstack -Wall -Wa,--noexecstack -g -O2 -fdebug-prefix-map=/build/openssl-7zx7z2/openssl-1.1.1f=. -fstack-protector-strong -Wformat -Werror=format-security -DOPENSSL_TLS_SECURITY_LEVEL=2 -DOPENSSL_USE_NODELETE -DL_ENDIAN -DOPENSSL_PIC -DOPENSSL_CPUID_OBJ -DOPENSSL_IA32_SSE2 -DOPENSSL_BN_ASM_MONT -DOPENSSL_BN_ASM_MONT5 -DOPENSSL_BN_ASM_GF2m -DSHA1_ASM -DSHA256_ASM -DSHA512_ASM -DKECCAK1600_ASM -DRC4_ASM -DMD5_ASM -DAESNI_ASM -DVPAES_ASM -DGHASH_ASM -DECP_NISTZ256_ASM -DX25519_ASM -DPOLY1305_ASM -DNDEBUG -Wdate-time -D_FORTIFY_SOURCE=2
OPENSSLDIR: "/usr/lib/ssl"
ENGINESDIR: "/usr/lib/x86_64-linux-gnu/engines-1.1"
Seeding source: os-specific
With that out of the way, next make sure you’ve got the prerequisites ready and sorted as listed below. Then follow the steps provided.
OpenSSL CSR generation: prerequisites and steps
With regard to the necessary OpenSSL CSR generation prerequisites, ensure you that have the following items before beginning the process:
- Root or sudo access to the user account.
- A terminal or command line window open.
- An established SSH connection (if working on a remote server).
- OpenSSL installed on your system to produce the key.
- A Text editor to view the private key and CSR.
OpenSSL CSR generation step #1: start terminal mode for your operating system
To start OpenSSL CSR generation, you will need to use the terminal. If you have Windows, follow wikiHow’s instructions. If you’ve macOS, follow instructions from Apple.
OpenSSL CSR generation step #2: generate RSA private key and CSR
Follow the steps below to generate RSA (Rivest–Shamir–Adleman) private key and CSR.
Step #2a
In your local terminal, create a new directory based on the domain name by entering the following:
mkdir [mydomain]
Replace “mydomain” with your domain name.
Step #2b
Change the directory to the newly created directory by entering:
cd [mydomain]
Replace “mydomain” with your domain name.
Step #2c
Run the command below to generate a CSR and a private key. You may copy-paste this code into the terminal to speed things up.
Pseudo code snippet example
openssl req -new -newkey rsa:2048 -nodes -keyout server.key -out server.csr
Code snippet example
openssl req -new -newkey rsa:2048 -nodes -keyout mydomain.key -out mydomain.csr
Creating a separate directory for every CSR and key helps you locate the files easily. The commands are broken down as follows:
- openssl — activates OpenSSL.
- req — requests for a CSR.
- –new –newkey — generates a new private key.
- rsa:2048 — this command creates a 2048-bit RSA encryption key.
- –nodes no DES — do not encrypt the private key in a PKCS#12 file.
- –keyout — indicates the domain you’re generating a key for.
- –out — specifies the name of the file your CSR will be saved as.
Note that using 2048-bit key pairs is recommended. While the 4096-bit key pairs are more secure, they require more server resources.
OpenSSL CSR generation step #3: enter your CSR information
Upon running the OpenSSL command, your system will launch a bunch of text-based questionnaires for you to fill out with prompts. Answer each question by entering the required information:
- Country Name — use a 2-letter ISO country code for where the organization is located — US for the United States.
- State — the full name of the state where the domain owner is registered.
- Locality — the city’s full name in which the domain owner is registered.
- Organization Name — the legal name of the business entity or company.
- Organizational Unit Name — the department in your company responsible for SSL certificates — for example, IT or Security.
- Common Name — the Fully Qualified Domain Name (FQDN) of your website. If you’re generating the CSR for a wildcard domain, use an asterisk (*) in place of the subdomain name: *.example.com.
- Email Address — the webmaster’s email address — this is optional.
- Challenge Password — an optional password for your key pair.
- Optional Company Name — this can be skipped.
The Organization Name and Organization Unit Name values shouldn’t contain any of the following characters:
< > ~ ! @ # $ % ^ * / \ ( ) ? . , &
Review the following video as an example of the data entry process:
OpenSSL CSR generation step #4: locate CSR and the private key file
Once you enter all the CSR information, the application will create the CSR and the private key in the current working directory.
In this example, the OpenSSL command was run in the “mydomain” directory, so you can list the contents using the ls command:
ls *.csr
OpenSSL CSR generation step #5: submit the CSR as part of your SSL request
With the CSR and private key in hand, you can view them using cat or nano editor. Enter the following command to view with the nano editor:
sudo nano mydomain.csr
Or you can use the following command to view with the cat editor:
cat mydomain.csr
Review the following image example of using the cat mydomain.csr command:
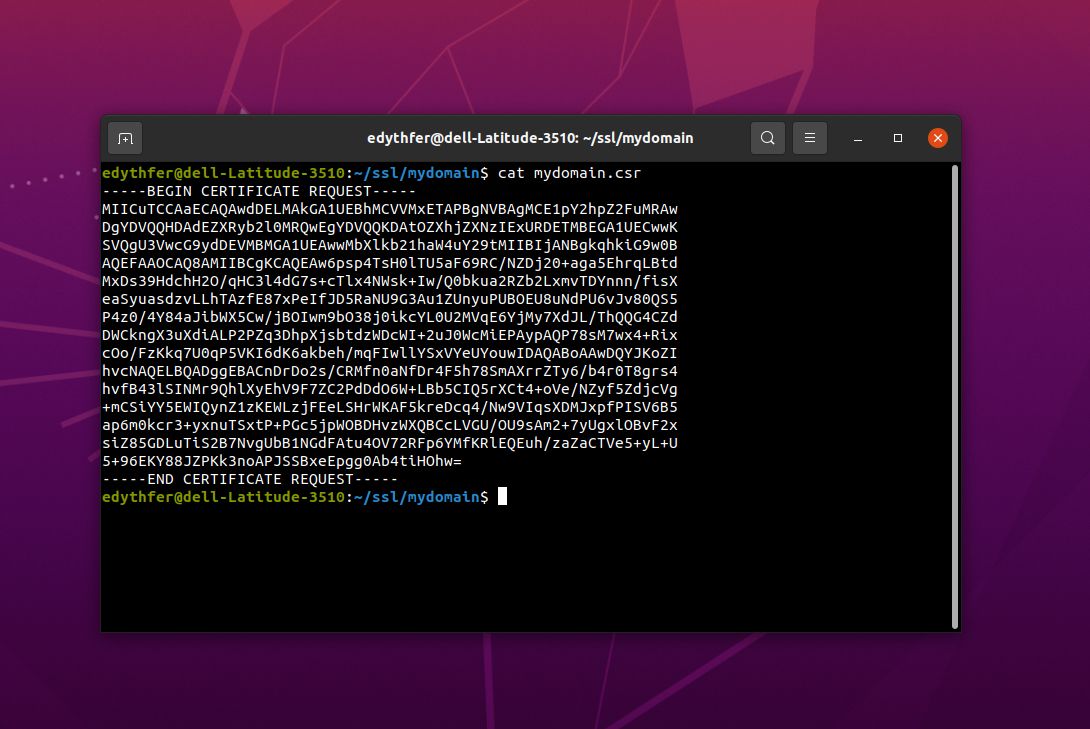
Copy and paste the entire block of characters into a submittal form for the SSL certification or into a Notepad text file — by copying all of the text including beginning and ending syntax lines:
-----BEGIN CERTIFICATE REQUEST-----
<<< entire block of characters >>>
-----END CERTIFICATE REQUEST-----
Some Certificate Authorities (CAs) may also let you upload the .csr file directly.
Your private key doesn't need to be sent to the SSL vendor. Instead, once you receive your SSL certificate, your server's private key will bind with it to encrypt communications.
Conclusion
SSL enhances security between a website and its users and protects sensitive data, such as credit card information, over the Internet.
Premium hosting products for every project
Working on a complex project? We recommend Liquid Web for total control and customization for your needs.
Now that you know how to generate a CSR using OpenSSL, we recommend you verify its contents before submitting the OpenSSL CSR to the certificate authority.
You can use an online CSR decoder such as SSL Shopper CSR Decoder.
How to skip the whole OpenSSL CSR generation process?
Do you want to skip the whole OpenSSL CSR generation process?
Get Managed Hosting from Nexcess and let our experts handle it. Or, check out Liquid Web's range of WordPress hosting, dedicated hosting, and VPS solutions.
We offer sophisticated technology stack optimized for the chosen content platform. Get performance and enhanced security from a rock solid web hosting provider when start today!
Recent articles
- Cloudflare firewall rules for WordPress
- Cloudflare WordPress setup for your CDN solution
- Cloudflare SSL with Cloudflare origin certificate



