WordPress is one of the most popular open-source content management systems (CMSs) for creating ecommerce, blog, portfolio, and other kinds of websites. Unfortunately, hackers are taking advantage of the fact that the WordPress code is open source.
So, it’s essential that you protect your website. In this article, we’ll show you how to secure a WordPress site to protect it from hackers, bots, spam, malware, and more.
The importance of WordPress security
Employing the proper security for a WordPress site protects your website from various cyberattacks. Both you and your clients’ private information will be protected with a secure website. Also, keep in mind that you protect your reputation by protecting your website.
Does WordPress offer inbuilt security?
By default, WordPress redirects all of the insecure HTTP requests (301 redirects) to the secure HTTPS version of your website. You can further protect your WordPress website by installing security plugins.
Use a WordPress security plugin
WordPress add-ons are a great way to quickly and efficiently add extra useful features to your website. One of the most critical add-ons you can install on your website is a security plugin. With just a few clicks, you add an extra layer of security to your website.

Some of the most popular plugins that provide security for WordPress sites are:
- Jetpack: This plugin is simple to install and offers comprehensive WordPress website security. Its features include real-time backup creation, spam protection, brute-force protection, and malware scans.
- Solid Security Pro: You can add an extra layer of protection to your website in seconds by installing this plugin. Solid Security Site Templates enable you to set the correct security settings for your ecommerce website in no time. You can monitor suspicious activities, scan for vulnerable plugins and themes to apply updates, block bots, reduce spam, and much more.
- Wordfence Security: This plugin includes a WordPress firewall, security scanner, and login security. It’s also user friendly.
Get secure WordPress hosting from Nexcess
All plans include free SSL certificates, daily backups, and Solid Security Pro
How to protect your WordPress site (checklist)
Now, let’s take a look at the steps you can take to secure your WordPress website.
1. Keep themes and plugins updated
Keeping your WordPress themes and plugins updated should always be number one on your WordPress security checklist. By doing so, you are actively protecting your website. Besides compatibility issues, older versions of WordPress themes and plugins can have dangerous security flaws that endanger your website.
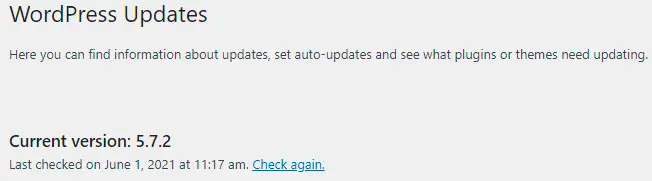
2. Make sure you’re running the latest WordPress version
According to W3Techs, about 43% of websites have WordPress as their CMS. This is why hackers are always searching for WordPress security flaws. It’s estimated that at least 13,000 WordPress websites are hacked daily.
So, having the latest WordPress version should be on your WordPress security checklist. Every time a security flaw is detected, the WordPress team starts to work on an update to patch up the issue. By keeping your WordPress updated, you ensure your website is stable and secure from hackers.
3. Use secure managed WordPress hosting
Before you even start thinking about how your WordPress website should look, you should choose a good hosting provider. Choosing a secure WordPress host is maybe the most crucial step on your WordPress security checklist.
Look for a hosting provider that offers good customer service, takes security measures seriously, and has the best features at your price point. A great option is managed WordPress hosting with Nexcess.
What makes Nexcess better than other hosting providers?
For one thing, your site loads extremely fast. Also, you get an integrated CDN, malware detection, site monitoring, and a built-in firewall that will keep your website free from well-known hacking attacks, such as distributed denial-of-service (DDoS) and brute force.
4. Set up a firewall
The chances of your WordPress website getting hacked drastically decrease if you have a firewall.
Common firewalls include:
- Apache Firewall: Includes a mod_security module that is widely used as a firewall.
- DNS (Domain Name System) Firewall: Protects your network from malicious domains and stops users from accessing malicious websites.
- WAF (Web Application Firewall): Controls incoming HTTP traffic and monitors and blocks potentially malicious connection attempts.
- NAT (Network Address Translation) Firewall: Only a device that is within a secure private network can access the server.
- Packet-filtering Firewall: Incoming requests are monitored based on the ports, protocols, and IP addresses.
5. Get an SSL certificate
An SSL (Secure Sockets Layer) certificate protects the integrity of your website and ensures secure online transactions with your customers. Once you have published your website, installing the SSL certificate should be the next step in your WordPress security checklist.
Next, activate HTTPS redirect, so visitors always access your website using the secured connection. The HTTPS protocol encrypts the data being transmitted between your hosting server and visitors. In other words, it secures all of the exchanged data.
6. Add extra security to the login page
Follow the next steps to protect your WordPress website through your login page.
1. Use a strong password
Numerous website breaches were successful due to stolen passwords. To prevent this, set a strong password that contains a minimum of 16 characters. Make sure that the password includes uppercase and lowercase characters, numbers, special characters, and separators.
Don’t use the same password for your wp-admin dashboard, databases, file transfer protocol (FTP) account, and hosting account. Hackers use bots to check if a password stolen from one online account is also used with other accounts.
You can easily create different strong passwords by using some of the numerous online password generators or by using WP User Manager.
Also, it’s best if you’re the only one accessing and maintaining your WordPress website. If you have to give access to other users, limit their access by disabling admin permissions for file editing. By doing so, your website will remain safe, and the content can be updated regularly by different users.
2. Limit login attempts
One of the best ways to protect your WordPress website from brute force attacks is to limit login attempts. The default WordPress settings allow unlimited login attempts. Hackers use this to their advantage by deploying password-guessing bots.
Depending on the servers and attackers’ resources, they can check from a few thousand up to a billion passwords per second.
That can be simply avoided by limiting login attempts. For example, you can temporarily block the user that had three failed login attempts.
Limiting login attempts is easy. All you have to do is install the Limit Login Attempts Reloaded WordPress plugin. A free version of the plugin will be sufficient.
Once you have installed the plugin, just open the settings and set up after how many failed attempts you want to block users.
3. Automatically log out inactive users
Hackers can use a cookie-hijacking method to breach your website. That is why it’s essential to set an auto-logout for all idle users.
The easiest way to implement the setting to automatically log out inactive users is to install the Inactive Logout plugin. Once you have installed the plugin, go to the plugin’s settings page and set after how many seconds you wish to log out the inactive user.
7. Back up your site regularly
One of the best ways to protect your WordPress website is to frequently back up your website and important databases. You don’t want to find yourself in a situation where your website is hacked or runs into a plugin theme conflict, and you don’t have a safely stored backup to restore it.
You can easily back up your WordPress website by using some of the free or premium WordPress backup plugins. Most of the free WordPress backup plugins will provide you with the basic one-click backup option.
Most of the premium WordPress backup plugins include:
- Automatic, scheduled, encrypted backups.
- Real-time backups, which back up your website after every modification.
- Database backups.
- Extra backup storage.
- One-click website cloning and migration.
- Third-party services integration for your backup storage.
- Additional security features, such as malware detection.
Some of the best WordPress backup plugins are UpdraftPlus, BlogVault, Duplicator, and Jetpack Backup.
Nexcess has an excellent backup policy. All of the Nexcess web hosting plans include free daily automatically created backups that are kept on a remote backup server. Your backups will be completely safe, as they’re accessible only by the Nexcess internal systems and the support team.
8. Change the admin username from the default
During WordPress installation, you will be asked to input your username. Never skip this part — make sure you choose a custom username. If your username is “admin,” then change it immediately. Using the default username makes you more vulnerable to brute-force attacks.
9. Use two-factor authentication (2FA)
No matter how strong your password is and how often you change it, there are numerous ways for it to be compromised. Using your password as a single method of authentication isn’t secure enough.
Numerous two-step authentication plugins are available on the WordPress website. Two-factor authentication plugins are easy to install and use.
Some of the most popular ones are:
10. Turn off file editing
From the wp-admin dashboard, you can edit files, themes, and plugins. If someone with malicious intent gains access to your files, your website will be in danger. So, you should turn off file editing.
This can be done in a matter of seconds with a bit of code. Insert this into your wp-config.php file:
// Disallow file edit
define( ‘DISALLOW_FILE_EDIT’, true );
define( ‘DISALLOW_FILE_MODS’, true );If you don’t want to mess with code, some WordPress security plugins allow you to disable file editing with just one click. Examples include MalCare and All-In-One Security (AIOS).
11. Disable PHP file execution
Hackers can upload malicious files to your website and compromise it. But it’s simple to disable PHP (Hypertext Preprocessor) file execution in order to stop malicious PHP scripts from running.
All you need to do is create a .htaccess text file on your computer and insert the following code inside it:
<Files *.php>
Order Allow,Deny
Deny from all
</Files>Next, upload the .htaccess text file to your /wp-content/uploads and /wp-includes directories with an FTP client or via the FileManager application in your cPanel dashboard. Doing so will prevent PHP files from running in those directories.
12. Secure your database
The WordPress database is the center of a WordPress website. It stores just about everything found on a WordPress website, from posts and pages to users and other custom website options. So, WordPress databases are one of hackers’ biggest targets.
Follow these steps to secure your WordPress database:
- Change the default admin username if you skipped it during installation.
- Limit user privileges.
- Change the default admin ID.
- Change the default database prefix.
- Always create backups before making any changes to the database.
- Delete custom tables if you remove a website extension.
13. Disable directory browsing
In order to disable an insight into the structure of your directories and file structures for other users, who could potentially search for potential security flaws, you should disable directory browsing.
All you need to do is add the next line of code into the .htaccess file, which you can find in the root directory of your WordPress installation:
Options All -IndexesBy disabling directory browsing, you have significantly reduced the possibility of your WordPress website being hacked.
14. Protect your .htaccess file
The .htaccess file allows you to control file permissions. This means that you can set the special access permissions for all of the files and file types. In order to protect your .htaccess file, go to your root directory and insert the following code.
Note that you need to activate the “show hidden files” option in your cPanel File Manager to be able to see it:
<Files ~ "^.*.([Hh][Tt][Tt][Aa])">
order allow,deny
deny from all
satisfy all
</Files>The code you have inserted will block everybody who doesn’t have admin privileges from accessing the files starting with .hta and secure your .htaccess file.
15. Delete inactive themes and plugins
Old and unused plugins are full of vulnerabilities and can be easily exploited. To prevent hackers from exploiting your website this way, remove all of the themes and plugins you’re not using. Also, make sure you frequently update the ones you’re using.
16. Change the WordPress default login link
The default WordPress login URL is domainname.com/wp-admin. If you leave the login link at the default settings, it’s easier for hackers to deploy a brute-force attack.
If you have already limited login attempts, the default login link shouldn’t represent a big issue. But an extra layer of precaution is always a good idea.
17. Disable the XML-RPC protocol
The Extensible Markup Language remote procedure call (XML-RPC) protocol was first built to enable communication between WordPress and other systems. For example, if you were using a WordPress application on your mobile device, you were using the XML-RPC protocol.
Nowadays, the XML-RPC protocol is outdated, and the REST API enables WordPress to communicate with other systems.
The biggest disadvantage of using the XML-RPC protocol on your WordPress website is that it presents a security flaw. By limiting the login attempts into your WordPress, you haven’t limited the XML-RPC login attempts.
Even though WordPress plugins for disabling XMLRPC protocol exist, the protocol could be easily deactivated using the .htaccess file. Open your .htaccess file.
Right below the </IfModule>, insert this code:
# Start XMLRPC blocking
<Files xmlrpc.php>
Order Deny,Allow
Deny from all
allow from 127.0.0.1
errordocument 401 default
errordocument 403 default
errordocument 404 default
errordocument 411 default
</Files>
# Finish XMLRPC blockingIf you need to enable XML-RPC access for a specific IP address, you can simply add the IP address below allow from 127.0.0.1. For example:
# Start XMLRPC blocking
<Files xmlrpc.php>
Order Deny,Allow
Deny from all
allow from 127.0.0.1
allow from 192.168.1.1
errordocument 401 default
errordocument 403 default
errordocument 404 default
errordocument 411 default
</Files>
# Finish XMLRPC blocking18. Hide your WordPress version number
If hackers can see your WordPress version number, then they know upfront what security issues your website has. Because of this, most premium security plugins include an option for hiding your WordPress version number.
Nevertheless, you can easily hide your WordPress version number by adding the next line of code into the functions.php file that can be found in your theme directory:
remove_action('wp_head', 'wp_generator');Protect your WordPress site from vulnerabilities
Now that you’ve gone over our WordPress security checklist, you know how to secure a WordPress site. Make sure you keep everything updated, change all of the passwords as frequently as possible, and regularly scan your local devices for malware.
Looking for a secure hosting provider for your WordPress website? Then check out managed WordPress hosting from Nexcess.
We make it easy and affordable to set up your website, and our customer support team is always available. Check out our hosting packages and contact us to get started today.