Magento 2 makes it easy to build an ecommerce store and sell globally. But this ease of use comes at a cost. Store owners aren’t webmasters and don’t always know how to secure a Magento site from security risks and cyberattacks.
You may be wondering, is Magento secure? And for good reason.
A security breach can result in expensive lawsuits, crippling fines, and permanent loss of reputation. A 2021 report by the Ponemon Institute found that the average cost of a data breach is approximately $4.24 million globally.
Do you want to learn how to secure a Magento website?
Here’s what you need to know:
- How To Secure a Magento Website in 4 Ways
- Popular Magento 2 Security Extensions
- Final Thoughts: How To Secure a Magento Site
Get fully managed Magento hosting
Accelerate your store's potential, without the tedious maintenance
How To Secure a Magento Website in 4 Ways
Is Magento secure? Yes, but only if you follow Magento security best practices. Operating an online store without securing it can lead to a data breach. Here are four simple Magento security tips to help you curb cyber threats.
1. Secure the Server Environment
A Magento store is only as secure as its weakest link. As a platform that relies on several technologies such as PHP, MySQL, and Elasticsearch, Magento is susceptible to compromise from multiple sources.
A vulnerability in any of its associated applications can compromise your online store. Therefore, before you secure your Magento installation, secure its associated applications and hosting environment.
Here’s how:
- Use SSH and SFTP to access your remote servers over an encrypted connection.
- Use unique and strong passwords for each application.
- Change passwords every three to six months.
- Set secure filesystem permissions with core Magento files set to read-only.
- Check access and error logs regularly.
- Set up local and remote backups for better reliability.
- Modify the Magento docroot to improve security.
- Use a web application firewall.
Once you’ve secured the Magento hosting environment, you can move on to securing the core application.
2. Apply Security Patches on Time
The best way to secure your Magento store is with security patches. These patches help protect your store from security loopholes without risking the compatibility issues of an upgrade.
Adobe recently identified critical vulnerabilities affecting Magento Commerce and Open Source versions 2.3.3-p1 to 2.3.7-p2 and 2.4.0 to 2.4.3-p1. It released two security patches, MDVA-43395 and MDVA-43443, to resolve the security vulnerabilities.
Applying a security patch is easy. You only need command line access to the Magento server and you’re good to go.
Here’s how to secure a Magento website by applying the latest security updates:
1. Upload the Magento security patch file to the Magento root directory.
2. Run the following command:
<pre><code>
$ patch -p1 < %patch_name%.composer.patch
</pre></code>
If “-p1” doesn’t work, try “-p2” instead.
3. Refresh the Magento cache from the CLI using:
<pre><code>
$ bin/magento cache:clean
</pre></code>
Make sure you test all patches in a staging environment before applying them to your production server.
3. Configure & Enforce Two-Factor Authentication
The Magento admin holds all your store data, including customer data and order information. To help merchants protect this information from unauthorized access, Adobe introduced Two-Factor Authentication (2FA) in Magento versions 2.4 and above.
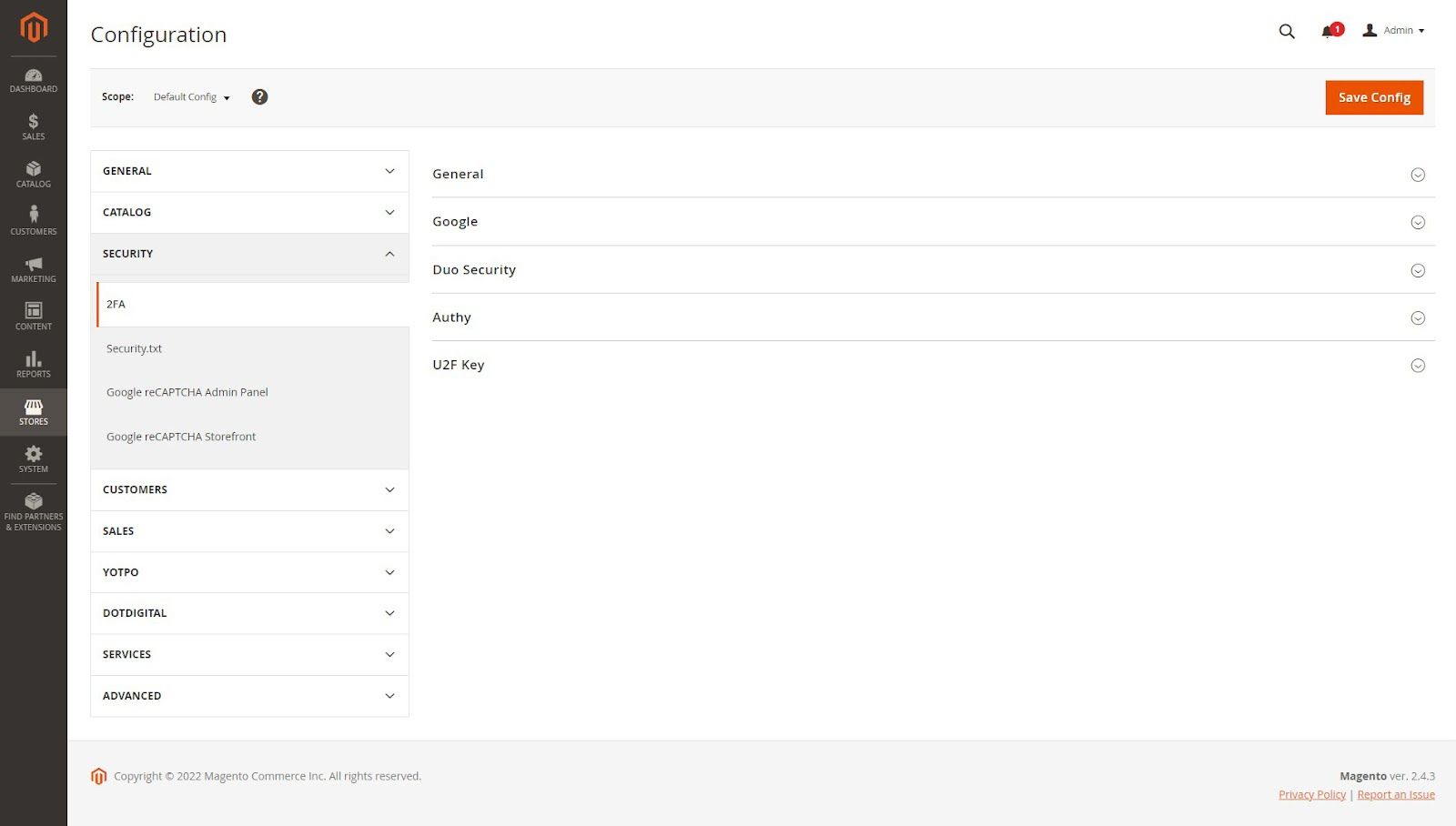
Magento’s 2FA security module supports authentication using Google Authenticator, Authy, Duo Security, and Universal 2nd Factor devices such as Yubikey. You can enable them in the Magento admin panel from Stores > Settings > Configuration > Security > 2FA.
You can also force a global authenticator for all admin accounts by navigating to Stores > Settings > Configuration > Security > 2FA and following these steps:
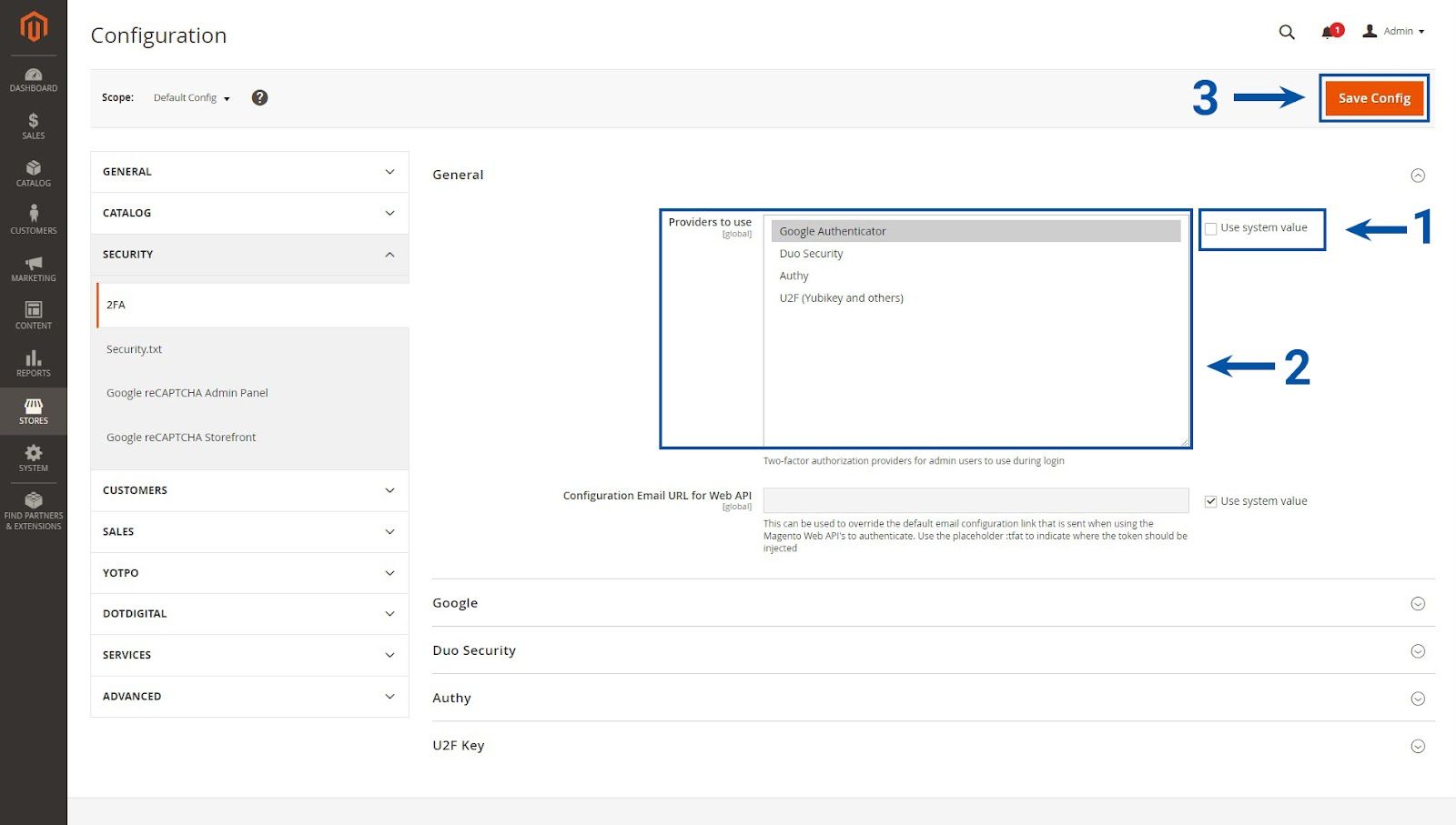
1. Expand the General section, uncheck the Use system value checkbox.
2. Select a provider from the Providers to use section.
3. Click Save Config.
4. Change The Encryption Key Frequently
Magento 2 uses an encryption key to encrypt sensitive information. It uses the industry-standard AES-256 (Advanced Encryption Standard) algorithm to encrypt data such as payment and integration passwords and SHA-256 (Secure Hash Algorithm) for all other data.
The Encryption Key tool in the Magento admin can and should be used to change the encryption key intermittently and in the event of a security breach. That ensures hackers can’t decode your encrypted store data should they gain access to it.
Are you wondering how to secure a Magento site by changing its encryption key?
It’s easy. First, update the file permissions for the app/etc/env.php file and make it writable. Then, go to System > Other Settings > Manage Encryption Key in the Magento admin and follow these steps:
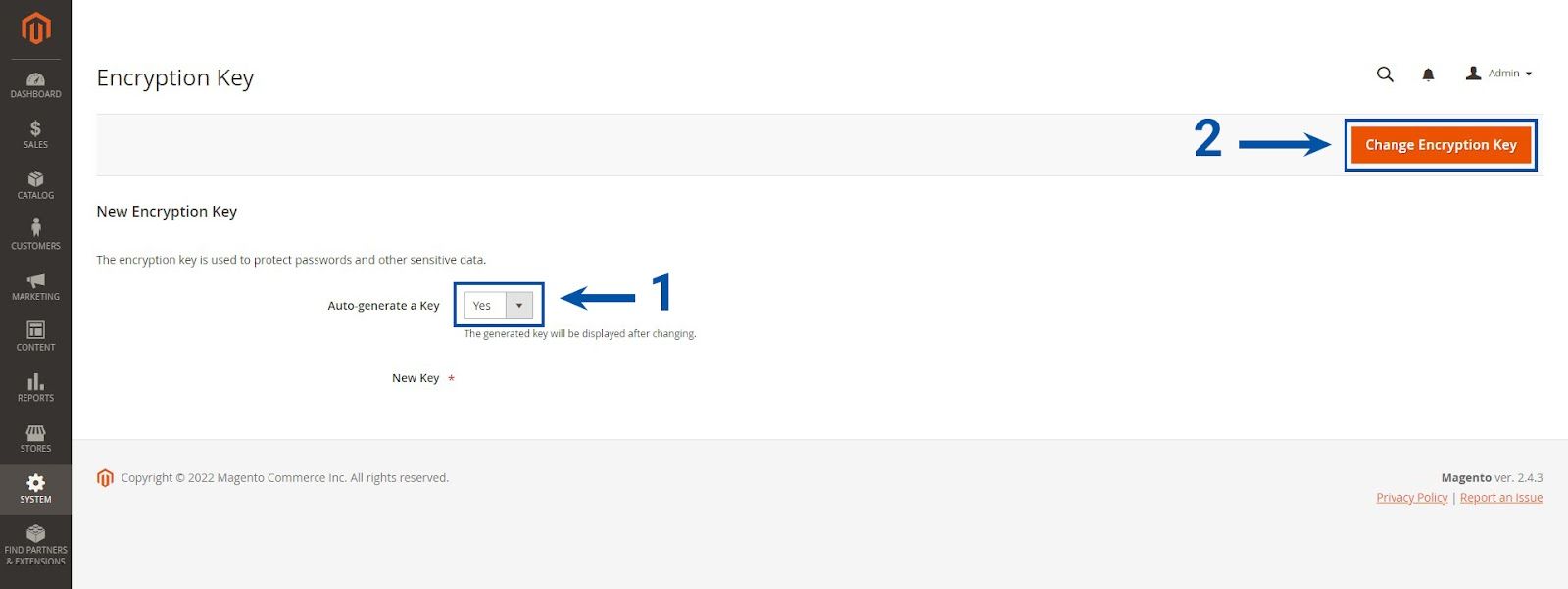
1. Set the Auto-generate Key option to Yes.
2. Click Change Encryption Key.
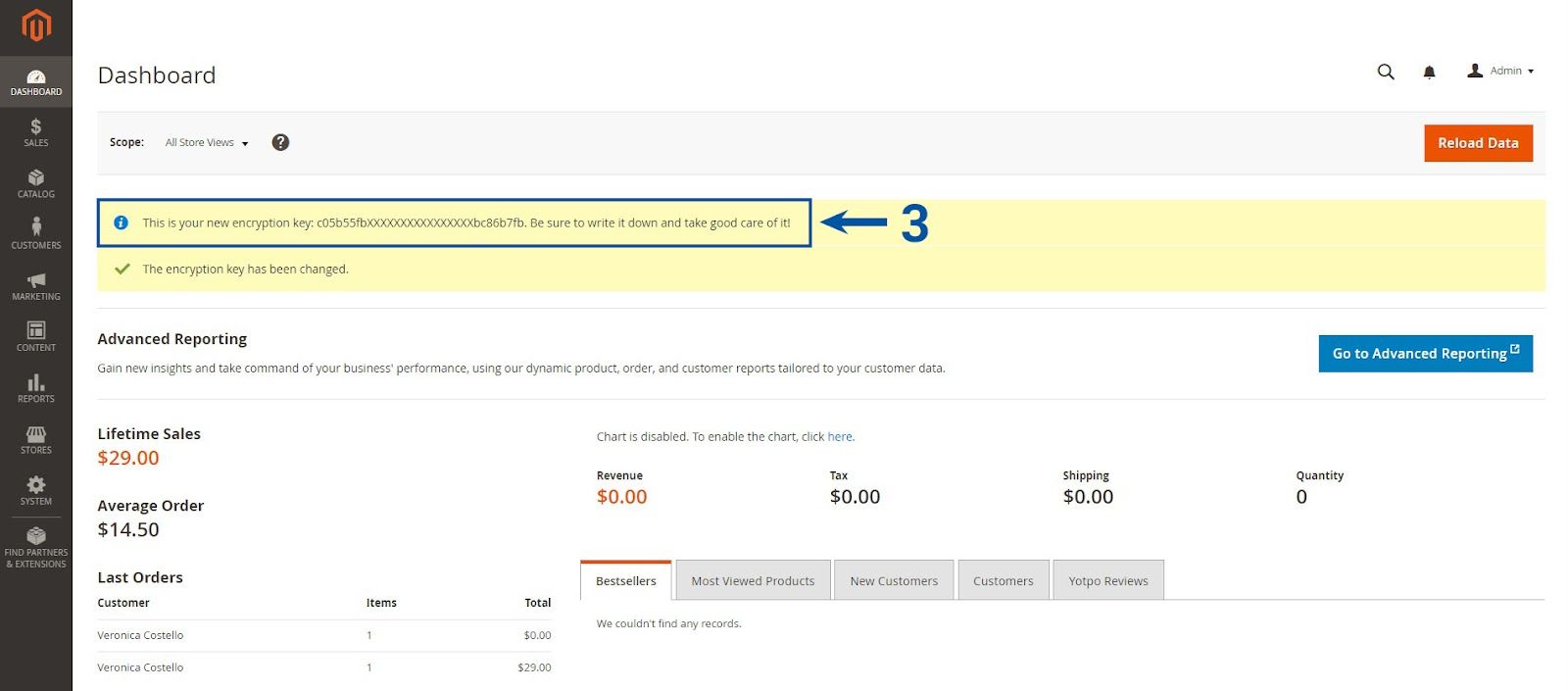
3. Copy the new encryption key and save it in a safe location.
Make sure you change the app/etc/env.php file permissions to read-only when you’re done.
Popular Magento 2 Security Extensions
Using a Magento 2 security extension doesn’t guarantee online security. However, it can help simplify securing your Magento store. Here are three popular Magento 2 security extensions you can consider.
1. Security Suite for Magento 2 by Amasty
Security Suite for Magento 2 helps you monitor admin activity and protects your store from spam and bots. It also includes 2FA support for an extra layer of security and allows you to manage user permissions.
Price: $419 for the first year and $255/year after that.
2. Magento 2 Security by Mageplaza
The Mageplaza Magento 2 Security extension keeps the bad guys out of your store with features such as a security checklist, brute force protection, login logs, and file change detection to identify suspicious activity.
Price: Community at $99 and Professional at $149 for the first year.
3. Watchlog by Wyomind
Watchlog by Wyomind is a free Magento 2 security extension that tracks traffic on the backend of your Magento site and protects it from brute force attacks. Its paid version, Watchlog Pro, adds blacklisting, automation, and reporting functionalities.
Price: Free, Pro at $151.
Final Thoughts: How To Secure a Magento Site
So, is Magento secure? It can be if you take the proper precautions. After all, business owners aren’t online security experts. And the rapidly evolving threat landscape makes it challenging to secure Magento from exploits. Basic security best practices such as SSL certificates and a unique admin URL can only take you so far.
We’ve shown you how to secure a Magento site in four ways. Besides these tips, you can also use the free Magento Security Scan tool to set up security alerts for common security threats.
Managed Magento hosting by Nexcess simplifies Magento store protection. Our plans include automatic malware monitoring, proactive security patches, and 30-day backups.
Sign up for a plan today.

